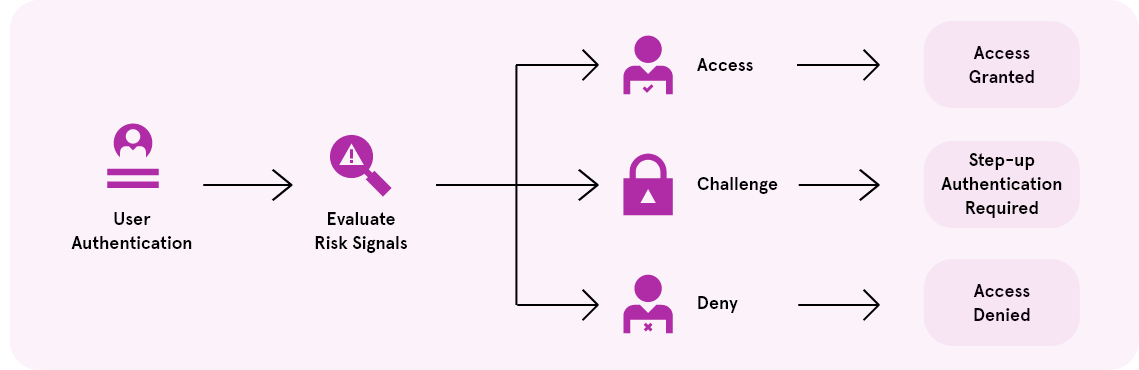
Risk Management
Enable your organization to make smarter authentication decisions. As a signal-based approach, risk management integrates into your authentication flows and policies to capture important characteristics of a user’s session.
This can include signals coming from a user, network or device. Signals are then aggregated to determine if an access request should be approved, be denied or require another login prompt.
How risk management works
MORE THAN RISK MANAGEMENT
MORE THAN RISK MANAGEMENT
Acquire and retain customers with seamless, secure and personalized digital experiences.
Acquire and retain customers with seamless, secure and personalized digital experiences.